Cisco has long said that it wants to network the world’s electricity grids much like it has networked the internet at large. But connecting computers, smartphones and other Internet Protocol (IP)-capable devices is a bit simpler than connecting power grid equipment that’s built around decades-old technology, as Cisco and other smart grid networking contenders have learned.
Indeed, connecting old grid gear via cutting-edge IP-based networks is a lot trickier than it sounds, requiring both the specialized chops to “translate” all those old utility technologies into a common framework, and the core networking skills to keep all that data traffic and control capability running smoothly -- and securely.
On Tuesday, Cisco launched a new set of substation automation products, along with operations and security expertise to back them up, that’s aimed at making this IP-to-grid transition a reality. It’s an interesting combination of some cutting-edge capabilities, including a virtual end-to-end IP network built on Multiprotocol Label Switching (MPLS) technology that can monitor and control old-school substation automation gear and protection schemes at the super-fast latencies required for the task.
At the same time, Cisco has unveiled a new security architecture and support system to make sure that newfangled capability doesn’t open up utilities to risks. In other words, if you’re going to network the grid via the internet, you'd better make sure you’ve locked down all the new access points and “attack surfaces” that this kind of integration opens up.
Building the End-to-End IP Smart Grid via MPLS
Cisco has already deployed its connected grid switches and routers with about 150 utilities around the world, and is deploying its new substation automation gear and IT with a few unnamed customers in Europe, Bradley Tips, senior product marketing manager for Cisco’s grid substation business, said in a Monday interview. The company is also integrating the new technology with big system integration partners, including French grid giant Alstom, as well as Cooper Power Systems and others, he said.
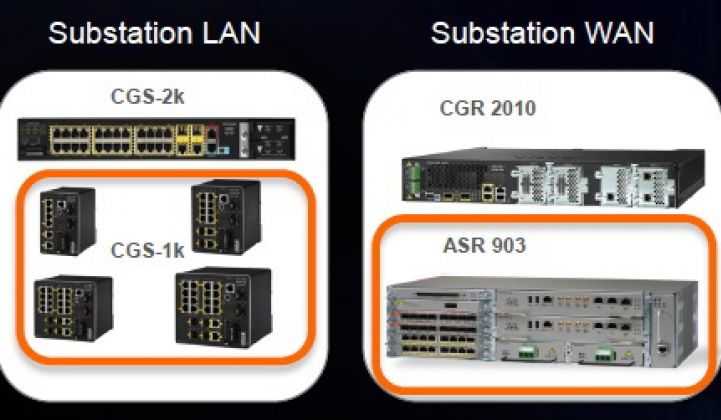
Cisco’s new products, the ASR 900 Series Aggregation Service Router and its 1000-series Connected Grid Switch (CGS) devices, make up the core of Cisco’s MPLS offering for the substation, he said. MPLS brings together a working mix of technologies that “translate” legacy grid gear protocols like GOOSE, DNP-3, Modbus, IEC 60870-104 and IEC 61850 into IP-compatible forms.
Cisco’s MPLS technology comes with some neat features that allow a new level of integration between the IP world and the legacy substation equipment world, Tips said. Those include features like “tunneling,” or converting serial-based SCADA data traffic into the packets at the heart of IP networking, he said.
Another neat trick is creating “pseudo-wires” that establish a connection between an end device and its control interface that appears, for all functional purposes, just like a direct wire connection between the two devices, he said. Those are the kinds of features that allow IP networks to achieve the super-fast, sub-10-millisecond one-way latencies needed to protect substations from the 60-cycles-per-second fluctuations of grid power.
Cisco’s not the only one promising MPLS for the grid, of course. Alcatel-Lucent, for example, has MPLS-based networks for utility transmission grids, and in December announced it was pushing those capabilities down into distribution grids and field-area networks, via its 7705 series Service Aggregation Routers. Right now, Cisco’s MPLS capabilities are focused on the substation, rather than on the feeders and circuits that make up the distribution grid itself, Tips noted.
Because almost all of these substation control and protections systems are already hard-wired, Cisco is also using the communications “pipes” already available for now, he said. But it also has an IPv6-capable wireless technology, via its 2010 acquisition of startup Arch Rock, which it’s using to link some substation gear in end-to-end IP networks, he said.
At the end of the road, the holy grail of deployments like these isn’t just in getting everything to work as smoothly on Cisco’s system as it did on the old legacy platforms, he observed. Instead, moving the substation to an IP-based framework is the first step in making future improvements and additions much easier and cheaper to execute, according to Tips.
In other words, instead of integrating all of these disparate grid systems via point-to-point application programming interfaces (APIs) or linking multiple systems into a common enterprise service bus (ESB), just make everything speak IP, and build from there. (Though that’s a lot more complicated than it sounds.)
Securing the IP-Based Smart Grid Network
That brings us to the matter of security. Every smart grid interoperability problem is also a security problem, Vikram Varakantam, Cisco senior solutions architect, said Monday. Much of the old legacy utility gear out there lacks the computing power or sophistication to carry even the most basic security features, he noted, putting the burden on the overlying network to maintain secure connections, detect and prevent attempts to exploit vulnerabilities, and the like.
Moving to an MPLS-based network helps with some of those tasks, while also opening up new challenges, Varakantam said. Cisco's existing Connected Grid Security architecture, launched Tuesday in conjunction with its substation offering, is meant to address these challenges using technology and techniques from the broader world of high-security networks, he said.
While cybersecurity is a complicated and multifaceted affair, Cisco has laid out a few core “principles” it’s adhering to in its new security architecture, Varakantam said. First comes access control, or limiting who can connect or communicate with individual endpoints on the grid. Second is device and platform integrity, which includes a “lifecycle approach” to managing Cisco’s grid systems, from deployment to end-of-life, he said.
The third focus area involves data integrity, confidentiality and privacy, which includes encryption, authentication and network traffic prioritization issues, as well as keeping data out of the hands of thieves or snoops. Finally, there’s threat detection and mitigation, which involves the task of discovering, isolating and eliminating attacks on the system, with the knowledge that no cybersecurity regime can be successful in preventing all intrusions all the time.
“With such a large attack surface on the utility side, you’re bound to have issues,” Varakantam said. “The real need is to detect and mitigate those in time, so that the infrastructure has time to rebound.” To support that effort, Cisco’s Security Intelligence Operation (SIO) is being made available to its utility customers, both to help them run ongoing security checks on its network and to help them comply with various regulations, such as North America’s NERC-CIP infrastructure protection requirements, which have recently been updated to include a lot more networked grid gear.
Cisco is also bringing the cybersecurity expertise of certain smart grid partners to bear on the problem, Tips noted. For example, partner Subnet Solutions is providing some application-layer security to help protect the networks that connect automation or protection schemes to substation end devices, he said. Physical security is also part of the picture, using Cisco’s networked cameras, sensors, card readers and underlying technology to do things like keep watch on remote sites or match worker ID codes to what’s being typed into gear in the field, he said.